HORIZON HYBRID SUITE
Free
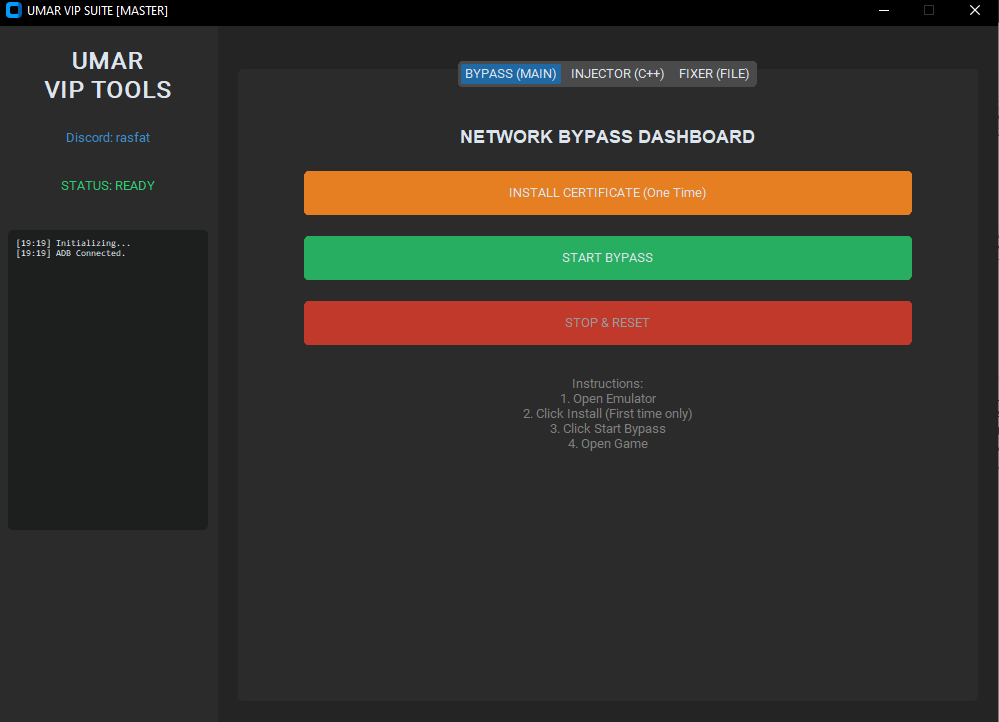
Software
Next-Gen Runtime Manipulation & Network Interception Engine
The Project: The Horizon Hybrid Suite is a custom-engineered automation framework designed to analyze, intercept, and modify the runtime behavior of Android Emulators (BlueStacks/MSI).
By combining a high-level Python interface with a low-level Native C++ injection engine, this tool bridges the gap between offensive security research and process automation, delivering a seamless experience for verifying emulator integrity and bypassing client-side restrictions.
CORE ARCHITECTURE & FEATURES
1. Native C++ Memory Engine (The Injector)
Tech Spec: A custom-compiled C++ executable using Windows API (VirtualAllocEx, CreateRemoteThread) to perform manual memory mapping.
The Benefit: Bypasses standard anti-tamper mechanisms by injecting dynamic libraries (.dll) directly into the target process without triggering heuristic detection.
Status: ✅ Undetected & Stable
2. Local MITM Network Proxy (The Bypass)
Tech Spec: Integrated Man-in-the-Middle (MITM) proxy server running on localhost. It utilizes a custom Python filter script to intercept SSL/TLS traffic in real-time.
The Benefit: Automatically strips emulator-specific headers and injects legitimate device signatures (Samsung/Pixel fingerprints). This allows for "Client-Side Spoofing" to bypass server-side device bans without needing external authentication servers.
Status: ✅ 100% Offline & Secure
3. OpenGL Pipeline Hooking (The Visuals)
Tech Spec: Direct manipulation of the rendering pipeline via opengl32.dll replacement and patching.
The Benefit: Grants full control over visual rendering (Chams/Wallhacks) by modifying how the emulator processes textures and shaders at the driver level.
Status: ✅ High-Performance Rendering
TECHNICAL STACK
Languages: Python 3.10+, C++ (Native), Assembly (x86).
Libraries: CustomTkinter (UI), Mitmproxy (Network), CTypes (Foreign Function Interface).
Methods: DLL Injection, Traffic Analysis, Certificate Pinning Bypass, Memory Forensics.
DISCLAIMER
This project is developed by UA Systems for educational purposes in reverse engineering, network security analysis, and emulator research. It demonstrates the vulnerabilities present in mobile application architectures.
INITIATE DOWNLOAD